So, how can you be sure your organization is doing the right things to prevent damage that can be caused by cyber threats and keep it within a small business budget?

Blog

So, how can you be sure your organization is doing the right things to prevent damage that can be caused by cyber threats and keep it within a small business budget?

As technology has evolved, cloud environments (commonly also referred to as SaaS, or Software as a Service) have become the backbone of business operations, offering scalability, flexibility, and remote accessibility. However, this shift has also exposed businesses to a new range of security threats.
Cybersecurity threats such as phishing attacks, ransomware, account takeovers, and data breaches can jeopardize sensitive information, disrupt operations, and damage a company’s reputation. For small to mid-sized businesses leveraging Office 365 and other cloud platforms, safeguarding their digital assets is critical to keeping your business up and running.
WorkSmart, partnering with cloud security company Avanan, can help protect your business by providing comprehensive cloud security solutions that protect against these evolving threats.
Although there are a myriad of threats that cloud environments can face, some of the most common ones we see in practice are based in a couple of categories.
Phishing attacks usually come in the form of emails, messages, or even phone calls that appear to be from a trusted source, such as a bank, a well-known company, or a social media platform. These messages often create a sense of urgency, fear, or curiosity to trick you into clicking on a link or opening an attachment.
Once you do, you might be taken to a fake website that looks incredibly real, where you’re asked to enter sensitive information like your password, credit card details, or social security number. Cybercriminals use these methods to trick users into revealing their credentials or downloading malware.
Ransomware is a type of malicious software that locks you out of your own computer files or entire system, and demands payment for their return. The attackers encrypt your files, making them inaccessible, and the key to decrypt them (or get them back to normal) is held for ransom, often demanded in digital currency, such as Bitcoin, to make the transaction harder to trace.
Ransomware can infect your computer if you accidentally download it by clicking on a malicious link in an email, visiting an infected website, or running infected software. Once it’s on your computer, it can spread rapidly, locking files not just on your own device but also on connected network drives, potentially affecting entire organizations. Paying the ransom doesn’t guarantee the return of your files and can even make you a target for future attacks, as it shows the attackers that you’re willing to pay.
An account takeover happens when someone else gains unauthorized access to your personal online accounts, such as your email, social media, or banking accounts. It’s like giving your house keys to a friend for safekeeping, but then someone else steals those keys without your knowledge. With those keys, or in this case, your account information, the thief can enter your “online house.”
They can pretend to be you, stealing your personal information, sending messages in your name, or even locking you out of your own account by changing the password. This can lead to a range of problems, from privacy breaches to financial loss. The intruder usually gets in by tricking you into revealing your password through phishing attacks or by guessing weak passwords, highlighting the importance of keeping your account details secure and using strong, unique passwords for each of your accounts.
A data breach is like someone breaking into a secure vault where companies store valuable information, such as customer names, addresses, credit card numbers, or even sensitive health records. Instead of physical thieves, these are cybercriminals who use sophisticated methods to bypass security measures and access this digital vault.
Once they have this information, they can use it for various illegal purposes, such as stealing identities, making unauthorized purchases, or selling the information to other criminals. For companies, it can result in significant financial penalties, loss of trust among customers, and damage to their reputation.
An insider threat is when someone from within an organization, such as an employee, contractor, or business partner, misuses their access to the organization’s systems and data for malicious purposes or personal gain.
Imagine an employee at a bank who has the keys to the vault and decides to steal money from it. Just like this employee, insiders with harmful intentions can access sensitive information, sabotage systems, or steal data because they are already inside the security perimeter, making them harder to detect.
This threat is particularly concerning because it comes from individuals who are trusted and have legitimate access, making it a complex issue for organizations to manage.
WorkSmart, partnering with Avanan, provides advanced security solutions specifically designed for cloud environments, including Microsoft 365 and Microsoft Teams, two of the most widely used platforms in the business world.
Our Microsoft 365 Protection solution offers a multi-layered approach to protect email, files, and collaboration tools across the entire suite. It employs advanced AI algorithms to detect and block phishing attempts, ransomware, and other malware before they reach the user’s inbox.
By scanning internal and external emails, we can help prevent account takeovers and safeguard sensitive data from unauthorized access. The seamless integration allows for easy deployment and management, ensuring you can maintain productivity without compromising on security.
As collaboration tools like Microsoft Teams become integral to business operations, securing these platforms is crucial. Our Teams Security solution protects against malicious files and links shared within conversations. It offers real-time scanning of shared content, detecting and blocking threats that could compromise the network.
Additionally, policy enforcement capabilities ensure that communications comply with regulatory standards and company policies, protecting against data leaks and insider threats.
Avanan stands out in the cloud security space for several reasons:
Are you ready to safeguard your business against the ever-evolving cyber threats that loom in the digital landscape? Protecting your sensitive data, customer information, and internal communications has never been more crucial.
With WorkSmart by your side, you can protect your business against phishing attacks, ransomware, account takeovers, insider threats, and data breaches, ensuring your peace of mind. Don’t wait for a security breach to disrupt your operations and tarnish your reputation.
Contact us today to learn how our comprehensive security solutions can be tailored to fit your unique needs, allowing you to focus on growing your business with confidence.
As technology has advanced over the years, so has cybercrime. Cyber security is essential for businesses because it serves as a preventive measure to protect online data.
In layman’s terms, cyber security consists of procedures used to safeguard a company’s essential information from any sort of cyber-attack or cyber threats. Over the years, cyber crimes have become more advanced as criminals are coming up daily with new ways to get sensitive information that includes using social engineering and AI. As companies adopt the latest technology, they must also heighten their cyber security to match it.
Cyber security is also referred to as IT security. For corporations, IT security is crucial in blocking cyber threats by stopping cyber criminals from getting a hold of a company’s assets.
Sustaining premium levels of cybersecurity can help you control your network resources while still fulfilling your business goals with no interference. As a business, it is critical to understand why cyber security is important for the safety of your organization.
Cyber security strategies act as protection against various cybercrimes including:
Cyber security is crucial for business growth. When considering security measures, these must be included:
Information theft is rapidly becoming the costliest division of cybercrime due to the exposure of important information in the cloud. It’s important to know that some cybercriminals only want to alter information, creating mistrust among employees and businesses.
Managing third-party risk helps businesses satisfy regulatory requirements. Here are some suggestions on other ways to avoid future cyber-attacks.
An excellent way to mitigate a cyber-attack is to educate your staff. IT security training is a viable technique used to aid employees in maintaining data security. Your workforce will learn the cyber dangers linked to their daily activities, potential cyber-attacks, and how to stay safe.
Privileged access denotes the methods used to manage permissions for accounts and users of the IT world. To decrease the risk of a cyber incident from an internal error or external perpetrator, employees are given access based on their job and job responsibilities.
Another way privileged access improves cyber security is it decreases the possibility of security breaches and human error.
Businesses must monitor their networks and systems 24/7, making sure there’s no suspicious activity. Cyber security monitoring can detect a cyber attack and respond immediately.
There are many reasons why cybersecurity is essential for businesses. Clients are increasingly becoming victims of fraud and hacking. Cyber security makes internet activities safe, as well as helps companies maintain brand reputation and keep employees safe.
Are you looking for comprehensive managed IT services in Charlotte, NC? Schedule a free consultation with us so we can talk.

“Your hardware has reached the end of its useful life.” As a business leader, you’ve likely seen this message before, but do you know what it actually means? Or how it can affect your business operations?

Passwords pose a major security risk to your organization. Even though most of us have always been taught to create complex and strong passwords, that doesn’t eliminate the threat of them getting guessed, stolen, or hacked.
As cyber criminals get more advanced in their tactics, the ways in which we protect our accounts must advance as well.

The shift to the cloud has become increasingly popular as it provides the accessibility businesses now need to work from anywhere. However, this also means that your data is much more at risk in the cloud if you don’t have the proper security tools in place.
Microsoft Azure Active Directory is an identity and access management service that combines user credentials and authentication policies to control who can log into your systems. No matter if your data is stored on a server in your office or in an app online – Azure AD protects it.
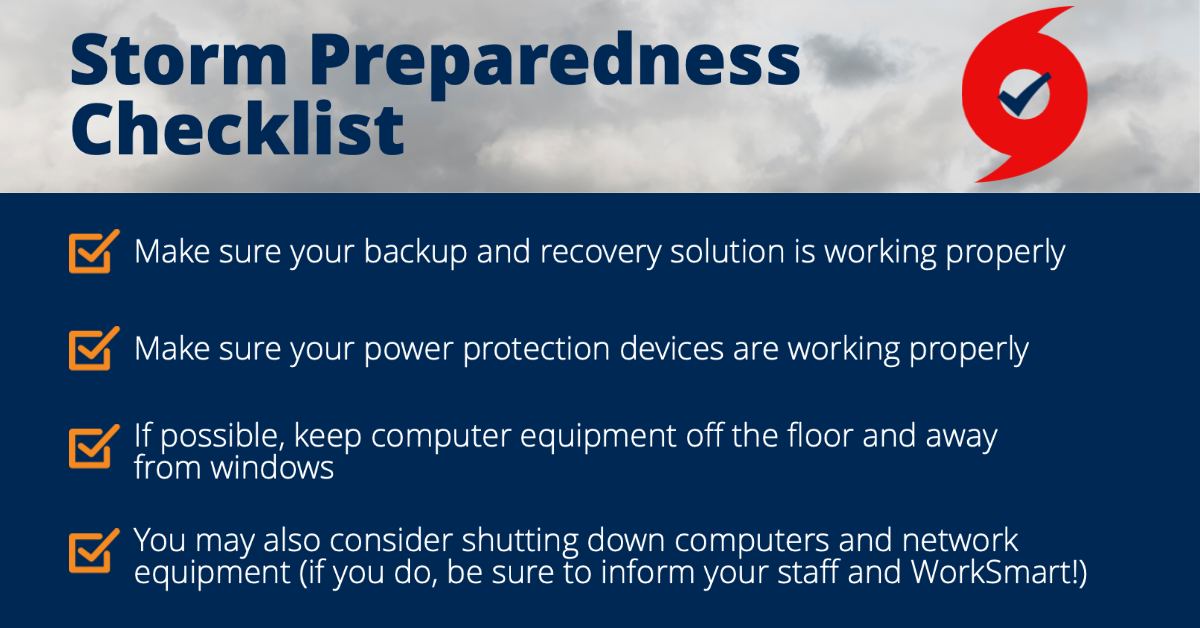
Whether it’s a snowstorm that knocks out the power or a hurricane that brings floodwaters – bad weather can have extremely unpredictable damage that ensues because of it.
When this happens, it’s important to make sure you take proper precautionary steps to help protect your IT infrastructure and data from the potential repercussions of a storm.

Over the past couple of years, we’ve likely all found ourselves in a position where we needed to get some work done, but our only internet option was public wifi.
Whether you like to head to your local coffee shop or get some work done in a bookstore, oftentimes there is no other option for you to use.

It’s officially Spooky Season, but no need to fear… we’re bringing you another Bytes & Brews webinar to help keep your business from getting spooked.
But, we’re doing it with a twist. We’re splitting our usual webinar into 5 short videos. Check them out below!
 |
Shoutout to our friends over at Capitol Coffee for providing an awesome swag bag for our registrant giveaway! “Family owned and locally roasted in Wake Forest, North Carolina, we are focused on one simple vision: To provide a moment of calm before the chaos with a unique tasting experience of evenly roasted, rich, full-bodied flavor in every sip. Lil’ Red is roasted in small batches. Our roasting process preserves the optimal flavor profile of our beans so that you receive the same high-quality coffee with every order.” |

It’s no secret that the risk of a cyberattack is high. As threats continue to evolve, it’s no longer a matter of if but when a threat will get past your security defenses. When that happens, you need to be prepared with a plan of action that not only identifies potential threats but also jumps into action to help minimize the damage done.
Fortunately, there is a proactive security solution that not only decreases your risk of being attacked in the first place but also saves your organization valuable time and resources should one manage to get through.
Continue reading for a look into our Managed Detection & Response security service and how it compares to other solutions.