When something breaks at your business, one question matters more than almost any other: how fast is someone going to show up?
We don’t mean “not show up” in the “we’re looking into it” sense, but actually show up – engaged, accountable, moving toward a fix.
Most businesses never think to ask their IT provider this question directly. They assume fast response is included. They find out otherwise at the worst possible moment – when a server is down, a team of fifteen people is sitting idle, and the ticket is sitting in a queue somewhere.
Before that happens to you, ask these five questions. They cut through the vague promises and tell you exactly what kind of support you’re actually getting.
1. Do You Have Defined Response Time Commitments – and AreThey inWriting?
A surprising number of IT providers operate on informal expectations rather than documented Service Level Objectives (SLOs). They’ll tell you they respond “quickly” or “as fast as possible” – but those aren’t commitments. They’re impressions.
What you want to see is a formal document – part of your agreement -that specifies exactly how fast the provider will begin working on different types of issues. Not resolve them, but start working on them.
If your provider can’t point you to a specific document with specific numbers, that’s your answer.
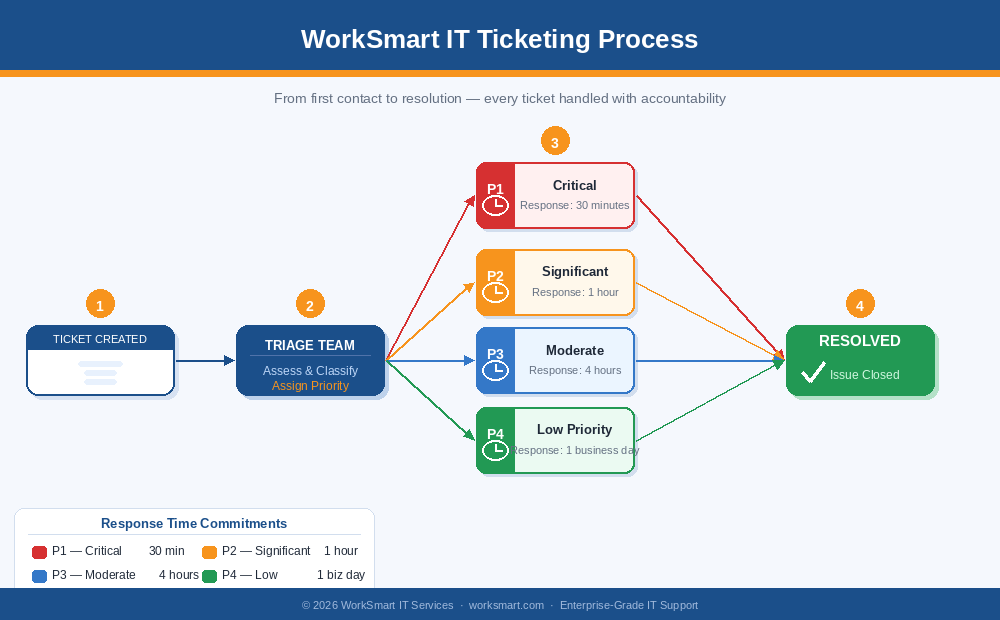
“Understanding the impact that our clients feel during different types of issues led us to overhaul our priority matrix and response times for each of the priorities with the goal of providing the most timely and efficient responses possible.”
Jason Kleiman, Vice President of Operations, WorkSmart
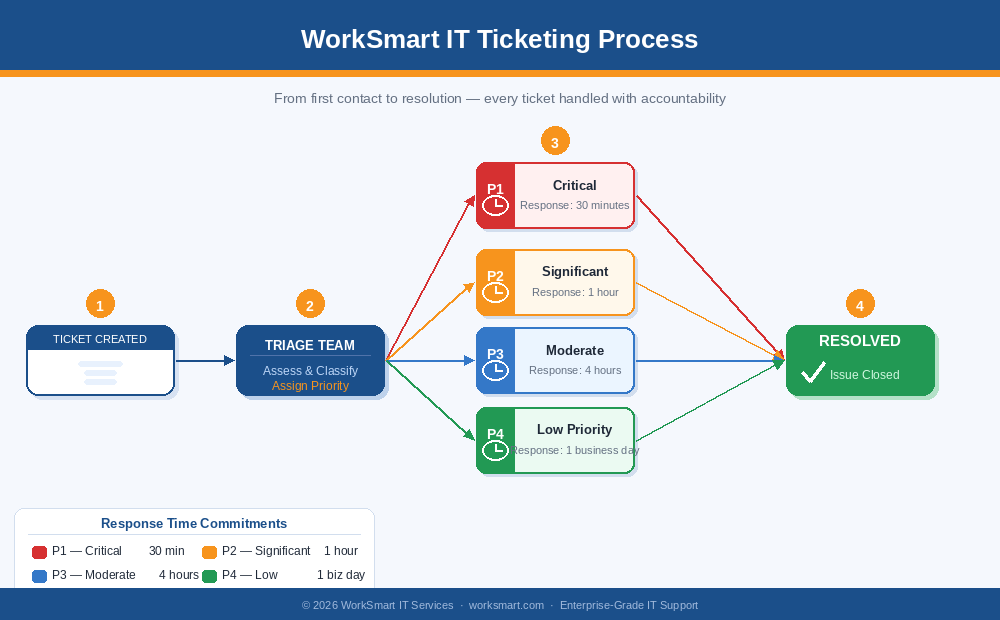
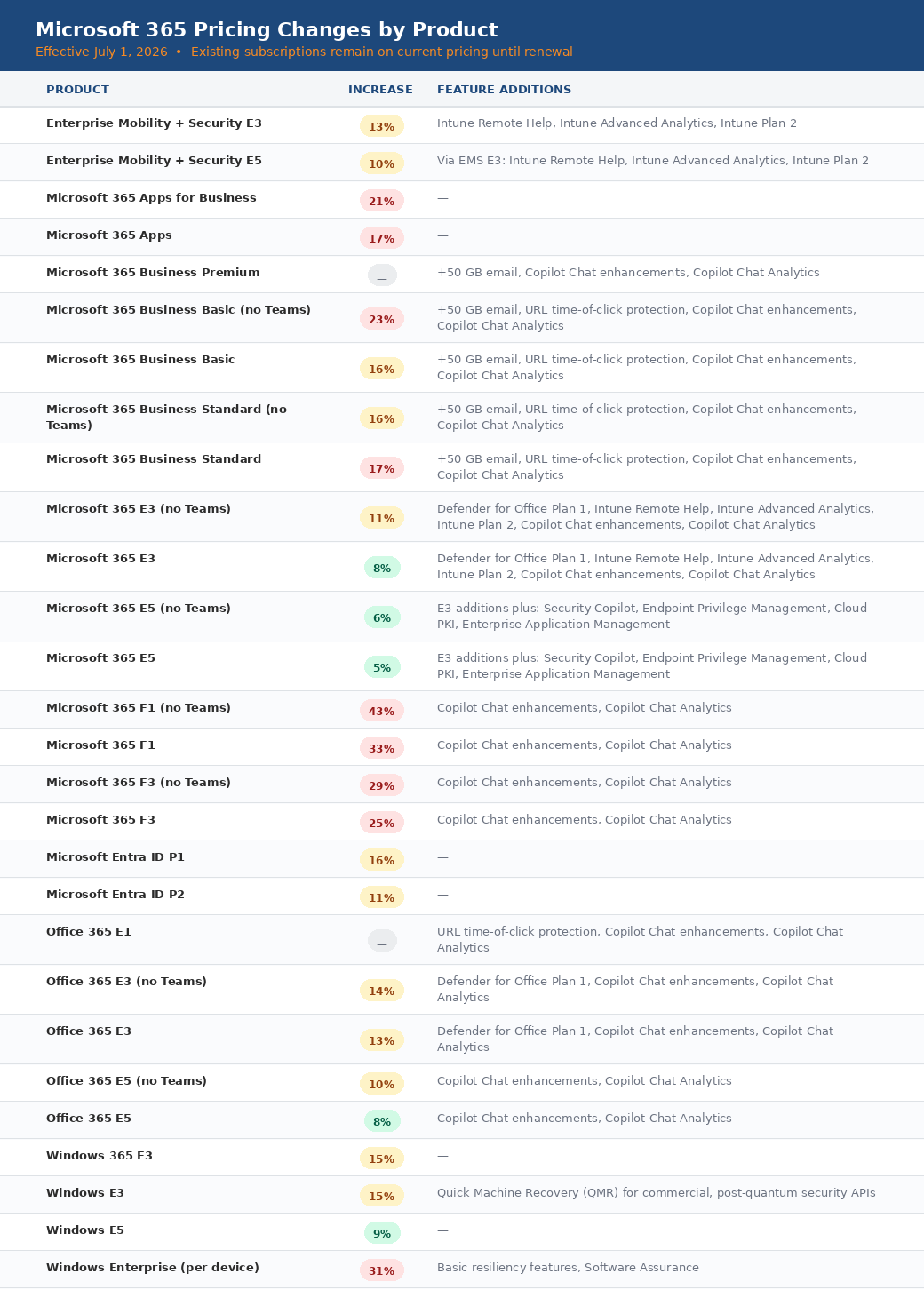
When a ticket is created, the clock starts ticking. There are 3 key checkpoints to all tickets:
- Triage – How long does it take to get the ticket assigned to someone
- Working Issue – A representative has actively started working on your ticket
- Resolved – Issue has been resolved
2. How Do You Define a Priority 1 Issue – and What’s Your Response Time for One?
Not all IT problems are equal, and good providers treat them differently. A company-wide outage that shuts down your entire operation deserves a fundamentally different response than a software glitch on one person’s machine.
The industry term for this is priority tiering – typically P1 through P4 – and what separates strong providers from weak ones is how clearly (and honestly) they define each level.
Ask directly: What qualifies as a P1 at your company? And what is your committed response time for one?
Enterprise-class IT support means responding to a critical, business-halting issue within 30 minutes. That’s the benchmark worth holding your provider to. If they’re quoting four hours for a P1- or they don’t have a clear answer at all – you have a meaningful gap in your coverage.
3. Can You Prove How Fast You Actually Respond?
This is the question that separates providers who have a process from providers who have a pitch.
Anyone can write a response time commitment into a contract. What matters is whether they’re actually hitting it – week over week, issue after issue – and whether they can show you the data.
Ask your provider: Do you track SLO performance? Can I see the numbers?
Providers who are genuinely confident in their operations will welcome this question. They’ll have reports. They’ll be able to tell you what their performance looked like last month across each priority level. Providers who hedge, deflect, or tell you the data “isn’t available in that format” are telling you something important.
Accountability requires visibility. If your IT company can’t show you how it’s performing, you have no way of knowing whether the commitment in your contract means anything at all.
“Accountability only works if it’s visible. We closely track our SLO performance every week and investigate any failures so that we can continue to improve, not because a client asked for it, but because the only way to get better is to know exactly where you stand.“
Jason Kleiman, Vice President of Operations, WorkSmart
4. What Happens When a Critical Issue Occurs Outside of Business Hours?
This one exposes more gaps than almost any other question.
Many IT providers staff robustly during the 9-to-5 window and go thin – or dark – everywhere else. That’s fine if your business only operates during those hours. But most businesses today can’t afford a multi-hour gap in coverage on a long weekend, during a holiday, or at 7 AM when the team is trying to start the workday and something isn’t working.
Ask specifically: If a P1 hits at 9 PM on a Friday, who respond, and how fast?
The answer should involve a real person, a real process, and a real time commitment. “We have an emergency line” is not the same as a structured after-hours support model with documented response times. Push for specifics, and listen carefully to how confidently – or vaguely – they answer.
5. When Did You Last Improve Your Response Time Commitments?
This question is less about the answer and more about what the answer reveals.
A provider who hasn’t revisited their SLOs in years is a provider who isn’t actively measuring their own performance or pushing themselves to get better. IT support is an operational discipline; it requires continuous refinement, regular review, and a genuine culture of accountability. Stagnant commitments usually reflect stagnant processes.
The best IT partners don’t just maintain a standard. They raise it. They look at their performance data, identify where they’re falling short, and make structural changes to close the gap. They rebuild their frameworks when the old ones aren’t good enough. And when they do, they tell their clients about it — because transparency is part of the service.
If your provider’s response is a blank stare or “we haven’t needed to change anything,” it’s worth asking yourself: are they actually measuring performance? Or are they just assuming everything is fine?
What Strong Answers Look Like
By the end of these five conversations, you should have a clear picture of whether your IT provider is operating with genuine accountability or coasting on assumptions.
Here’s what a strong answer looks like across all five:
- Written SLOs that are part of your agreement, not just a verbal assurance
- Clear priority definitions – P1 through P4, with no ambiguity about what qualifies
- Performance data your provider tracks and can share with you on request
- Documented after-hours coverage with the same response time commitments as business hours
- A history of improvement – evidence that the provider measures itself and raises the bar over time
Most providers can answer one or two of these questions well. Fewer can answer all five.
Why This Matters More Than Most People Realize
Response time commitments aren’t just an operational detail. They’re a signal about how a provider thinks about the relationship.
A provider who publishes clear SLOs, tracks performance against them, and shares that data with clients is a provider who understands that accountability isn’t just good ethics – it’s good service. When something goes wrong (and something always eventually goes wrong), you want to know that your provider has the processes, the people, and the culture to respond the way they promised.
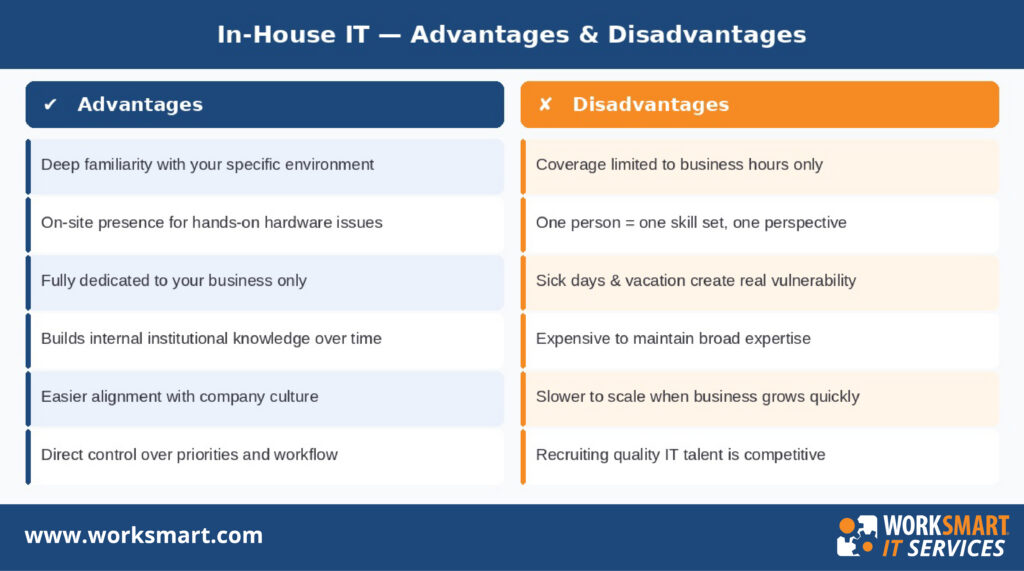
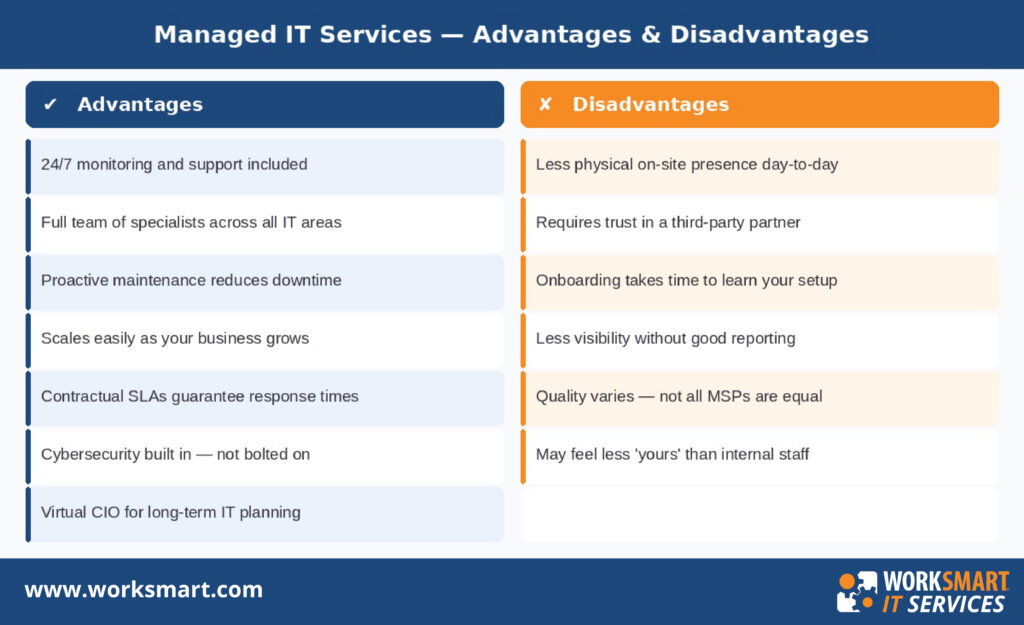
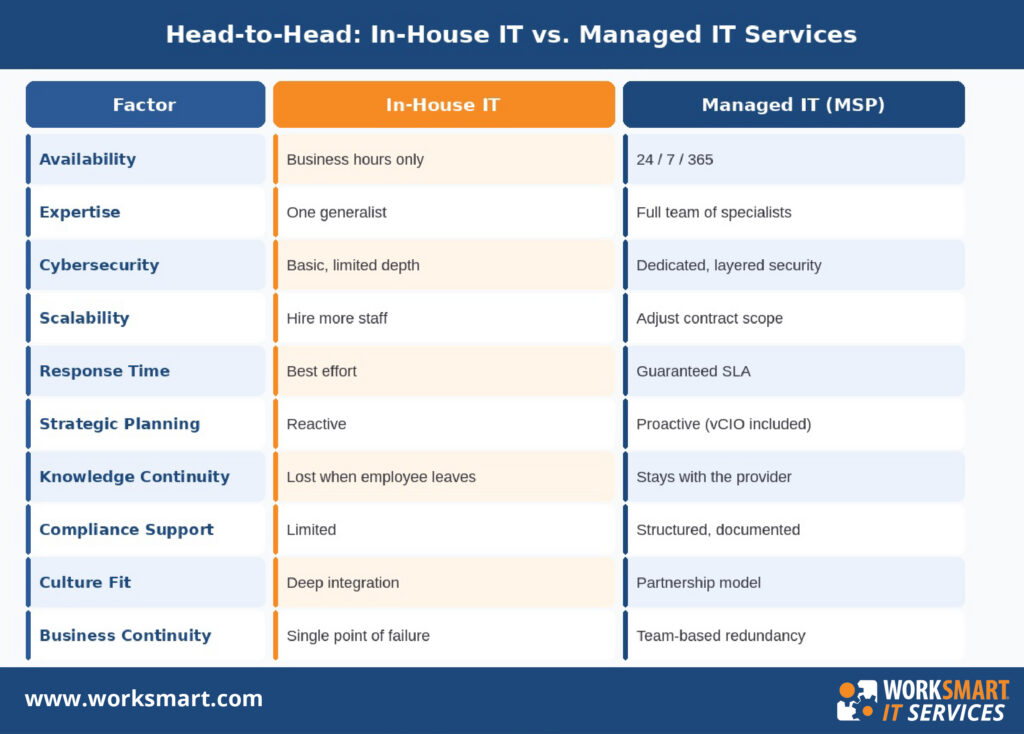
Still weighing your options on IT support? Our recent guide on In-House IT vs. Managed IT Services breaks down how the two models compare – including coverage, cost, and resilience – so you can make the decision with confidence.
The five questions above won’t guarantee a perfect IT partner. But they’ll tell you very quickly whether the one you’re talking to is serious about earning your trust, or just selling you on the idea of it.
“With our newly implemented SLO’s, our new priority matrix and a focus on live support, we are now operating a level we have never been able to offer our clients before”
Jason Kleiman, Vice President of Operations, WorkSmart
If you want to see what WorkSmart’s response time commitments look like, and how we hold ourselves accountable to them, we’d welcome the conversation.
Get a free consultation →
About WorkSmart IT Services
WorkSmart is a leading managed IT services provider serving small and mid-sized businesses across the Southeast. With offices in Charlotte, Raleigh, Durham, Greensboro, Atlanta, and Philadelphia, WorkSmart delivers enterprise-grade IT support, cybersecurity, cloud services, and strategic IT planning to growing businesses.
Frequently Asked Questions
What is an SLO in IT support? An SLO (Service Level Objective) is the specific, measurable performance target your IT provider commits to hitting. For support, this means a defined response time for each type of issue – Priority 1 through Priority 4. A clearly documented SLO framework tells you exactly how fast your provider will respond to a critical outage versus a routine request, and gives you a measurable standard to hold them to.
What is a reasonable P1 response time for a managed IT provider? For a business-critical issue — something actively preventing your team from working – enterprise-class IT support means an initial response within 30 minutes. Many providers commit to four hours or more for their highest-priority issues, which is a significant gap when a full team is sitting idle. When evaluating providers, ask specifically what their P1 response time is and confirm it’s documented in your agreement.
What is the difference between response time and resolution time? Response time is how long it takes a qualified technician to acknowledge and engage with your issue. Resolution time is how long it takes to fully fix it. SLOs typically govern response time, because resolution depends on the complexity of the problem. A strong provider commits to fast response and maintains transparent communication throughout the resolution process.
How do I know if my current IT provider is hitting its response time commitments? Ask them for performance data. Providers who track SLO compliance should be able to share reports showing how they’ve performed across different priority levels over a given period. If they don’t track this data – or won’t share it – you have no way of verifying whether their commitments are being honored in practice.
What should I look for in a managed IT services agreement regarding response times? Look for documented SLOs that specify response times by priority level, clear definitions of what qualifies as each priority, and language that outlines consequences if those commitments aren’t met. Vague terms like “as quickly as possible” or “best effort” are not commitments – they’re intentions. Your agreement should have specific numbers attached to specific scenarios.