It’s no secret that the risk of a cyberattack is high. As threats continue to evolve, it’s no longer a matter of if but when a threat will get past your security defenses. When that happens, you need to be prepared with a plan of action that not only identifies potential threats but also jumps into action to help minimize the damage done.
Fortunately, there is a proactive security solution that not only decreases your risk of being attacked in the first place but also saves your organization valuable time and resources should one manage to get through.
Continue reading for a look into our Managed Detection & Response security service and how it compares to other solutions.
What’s the problem?
Cyberattacks are more prevalent than ever, in particular for small businesses. A recent report shows that small businesses are three times more likely to be targeted by cybercriminals than larger companies. When a business is smaller, hackers assume that they don’t have a strong security posture, and therefore they become more of a target.
While technology continues to evolve, so do the cybercriminals that are constantly looking for loopholes and clever ways to hack into a system. Social engineering is an extremely effective way that attackers can manipulate users into willingly giving up sensitive information without realizing that they’re allowing a hacker in until it’s too late.
With cyberattack numbers remaining so high (and continuing to grow), it’s crucial that your business constantly adapts and improves your security posture to be as effective as possible in defending against these attacks. You’ve likely heard us say it before, but it’s not about finding the latest and greatest in technology to add to your system. But rather, it’s about finding the right solution to fit the security needs of your organization.
So, how do you do that?
A response plan that takes action.
5% of small business owners report cybersecurity to be the biggest risk to their business right now. As cybersecurity threats continue to increase in numbers, they’re also becoming more complex. A successful cyberattack in today’s environment can affect companies for years to come. Large amounts of money spent, a loss in productivity, and a hit to your organization’s reputation are only a few of the repercussions that can follow from a successful attack.
While you can never be completely resilient to a cyberattack, there are a few things you can do to help avoid cyber threats in the first place, and recover quickly should one get through your defenses.
In disaster situations, response time is key. A quick response to an attack can drastically decrease the impact that it has on your organization. The faster the threat is identified, the faster it’s able to be addressed, limiting the amount of damage that the attacker is able to do to your system.
You’re likely used to a security solution that is able to quickly identify threats, but that’s often the extent. The next steps are generally put into the hands of your team to determine the best course of action. While you may be able to address it quickly, the time it takes to hand off the situation can be the difference between you stopping a threat before it can do any damage and your organization having to pay millions for recovery.
The right disaster recovery solution should include both detection and response. While the first step is important in quickly identifying any potential security threats, the second step of actually responding to the threat is critical to ensuring that your organization can recover quickly. Having a team of experts waiting and ready to analyze any potential threat and determine the appropriate next steps not only minimizes the risk of downtime but it can also prevent your organization from losing valuable resources such as money, confidential data, and a good reputation. Plus, a security solution that includes that response aspect is often required to meet regulatory compliance and qualify for cyber risk insurance.
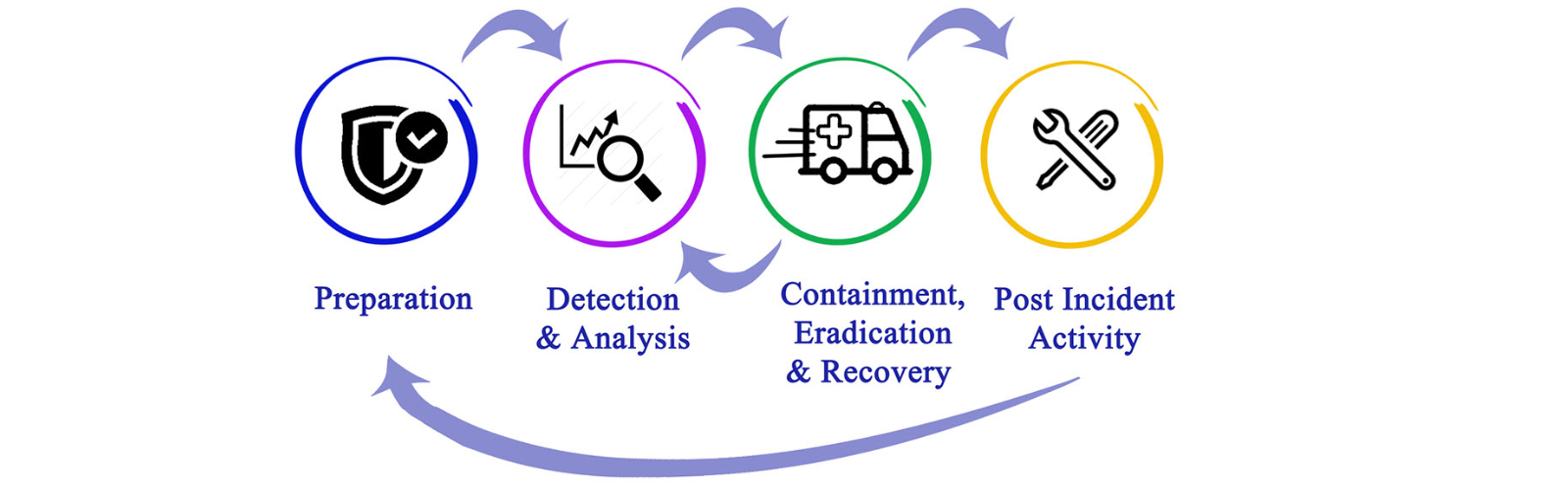
So, let’s take a look at how the process works.
How it works:
Our Managed Shield Anti-Virus with MDR works to identify and stop threats that have managed to bypass other cyber defenses. Built on Sophos Intercept X Advanced with EDR/XDR technology, MDR combines sophisticated (machine learning) technology and security expert analysis to find and neutralize active threats.
Step 1: Threat hunting
With 24×7 threat hunting, the Sophos team will hunt for and validate potential threats and incidents that could present danger to your organization.
Step 2: analyzing the threat
That team of security experts will take a closer look into any potential threats they identify and determine the scope and severity of threats.
Step 3: take action
With their full-scale incident response capabilities, the team will then take actions to remotely disrupt, contain, and neutralize any threats that pose a risk to your business.
Step 4: post-incident analysis
After critical actions are taken to mitigate the threat, the expert-led team will provide actionable advice for addressing the root cause of recurring incidents, helping your organization prevent them from happening in the future.
Improve your organization’s security posture.
Cybersecurity is not a one-time effort nor a one-size-fits-all solution. As technology changes regularly, it’s important to make sure that your business is continuously working to improve your security infrastructure and making sure that no vulnerabilities are left open for a potential attack.
WorkSmart’s Managed Detection and Response security solution (MDR) sets your organization up for success when it comes to leveling up your cybersecurity posture. Get ahead of the curve and protect your data before the issues arise.
Want to chat with someone to learn about how MDR could fit into your organization? Contact us below!



