Every growing business reaches a moment where the question becomes unavoidable: do we hire someone in-house to handle IT, or do we bring in a managed IT services provider?
It’s not just a budget question – it’s a question about control, culture, risk, and what kind of IT support your business actually needs to run well. Both models have real advantages. Both have real drawbacks. And the right answer depends on who you are as a business.
This guide breaks it down clearly so you can make the decision with confidence.
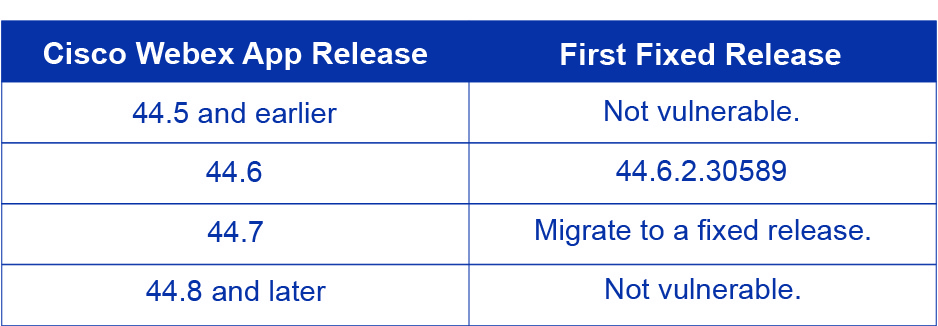
In-House IT: The Pros and Cons
Hiring a dedicated IT employee means having someone physically present in your office who knows your systems, your team, and your day-to-day operations. For some businesses, that familiarity is invaluable.
Advantages
- Deep familiarity with your specific environment
- On-site presence for hands-on hardware issues
- Fully dedicated to your business only
- Builds internal institutional knowledge over time
- Easier alignment with company culture
- Direct control over priorities and workflow
Disadvantages
- Coverage limited to business hours only
- One person = one skill set, one perspective
- Sick days & vacation create real vulnerability
- Expensive to maintain broad expertise
- Slower to scale when business grows quickly
- Recruiting quality IT talent is competitive
The Hidden Challenge: Depth vs. Presence
The biggest limitation of a single in-house hire isn’t commitment – it’s scope. IT today spans cloud infrastructure, cybersecurity, compliance, Microsoft 365, backups, networking, and end-user support. No one person is a deep expert in all of it.
When your in-house IT person reaches the edge of their knowledge – and they will – you’re calling in outside consultants at premium rates, often in the middle of a crisis.
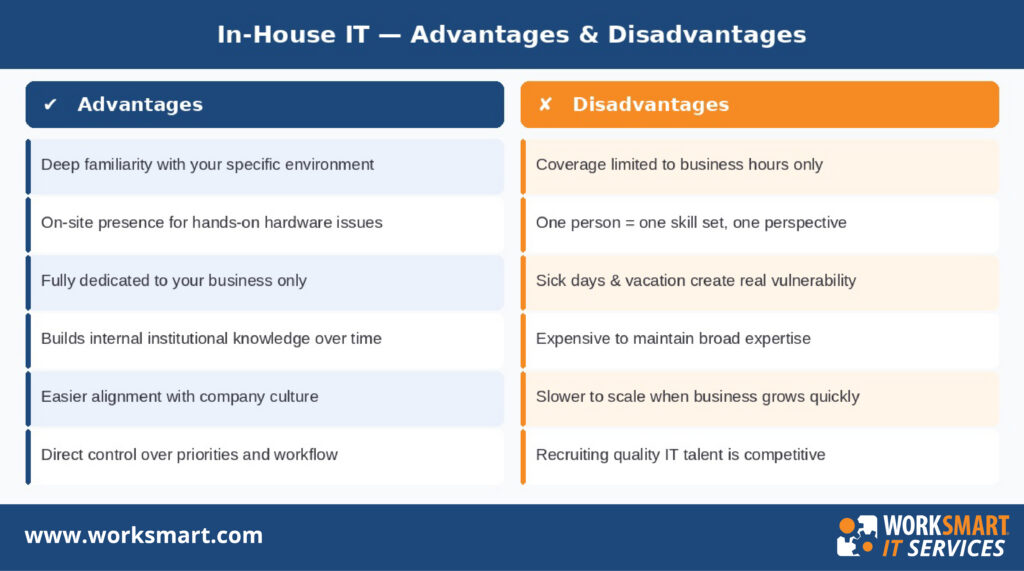
Managed IT Services: The Pros and Cons
A managed IT services provider (MSP) acts as your outsourced IT department. You get a team of specialists, 24/7 monitoring, defined response times, and a single point of accountability – all under one contract.
Advantages
- 24/7 monitoring and support included
- Full team of specialists across all IT areas
- Proactive maintenance reduces downtime
- Scales easily as your business grows
- Contractual SLAs guarantee response times
- Cybersecurity built in – not bolted on
- Virtual CIO for long-term IT planning
Disadvantages
- Less physical on-site presence day-to-day
- Requires trust in a third-party partner
- Onboarding takes time to learn your setup
- Less visibility without good reporting
- Quality varies – not all MSPs are equal
- May feel less “yours” than internal staff
The Core Advantage: Breadth and Resilience
When you work with a managed IT provider, you’re not relying on one person’s knowledge and availability. If your primary contact is on vacation, someone equally qualified picks up. If a threat emerges at 2 AM on a Saturday, the monitoring system catches it and a team responds – not a groggy employee getting woken up by a text message.
For businesses that depend on their technology to operate, that resilience isn’t a luxury. It’s a necessity.
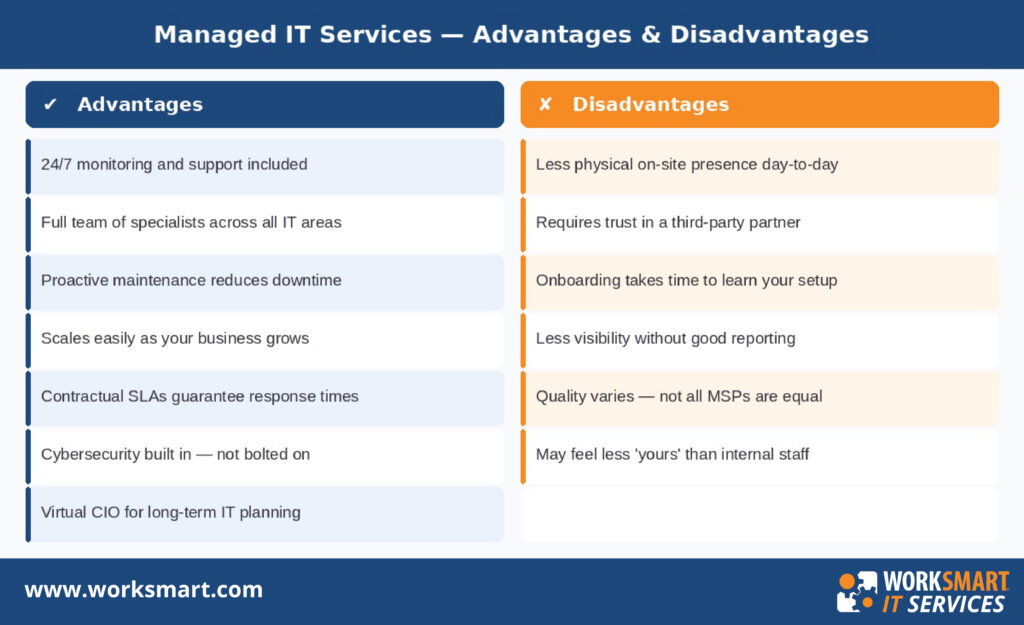
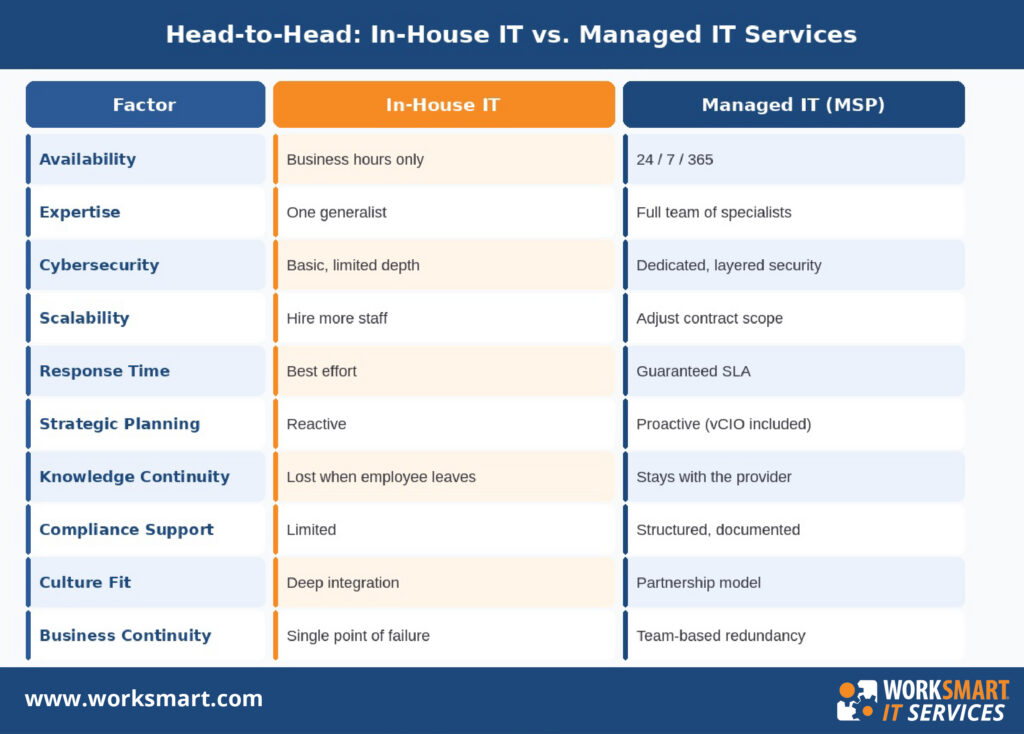
Head-to-Head: How the Two Models Compare
Here’s a quick reference across the factors that matter most to business decision-makers:
Which Model Is Right for Your Business?
Neither option is universally better. The right choice depends on your size, complexity, and what you need IT to do for your business.
In-House IT may be the better fit if…
- Your business has 250+ employees with complex, proprietary internal systems
- You operate in a highly regulated industry requiring a dedicated on-site compliance resource
- Your environment demands constant physical hardware management that can’t be handled remotely
- You already have an IT team and need headcount, not outsourcing
Managed IT Services may be the better fit if…
- You have under 250 employees and can’t justify – or fully utilize – a full IT department
- You’ve experienced IT problems after hours and had no one available to respond
- Cybersecurity and compliance are growing concerns but not currently well-addressed
- Your IT needs are growing faster than your ability to hire and train
- You want predictable, reliable IT support without the HR complexity of employment
Don’t Overlook Co-Managed IT
If you already have an internal IT person but need more coverage or specialized expertise, co-managed IT offers a middle path. Your internal team handles the day-to-day; an MSP provides the depth, tools, security layer, and after-hours support they can’t cover alone. It’s a model that’s gaining popularity among businesses that want the best of both worlds.
Questions to Ask Before You Decide
Work through these with your leadership team before committing to either direction:
- How often do we experience IT issues outside of business hours – and what happens when we do?
- Does our current IT setup have a cybersecurity strategy, or are we mostly hoping for the best?
- If our IT person left tomorrow, what would break – and how quickly?
- Are we growing? Will our IT needs look significantly different in 12–24 months?
- Do we need IT to be a strategic partner, or just someone who fixes things when they break?
Your honest answers will point you toward the right model more clearly than any general comparison can.
The Bottom Line
In-house IT offers presence and personal familiarity. Managed IT services offer breadth, resilience, and round-the-clock coverage. For most small and mid-sized businesses, the biggest risks – a security breach at 11 PM, an outage during peak hours, a key employee quitting – are exactly the scenarios that managed IT is built to handle and in-house IT struggles with most.
That doesn’t mean managed IT is right for everyone. But if you’re a growing business that depends on technology to operate, it’s worth taking a hard look at what your current setup can and can’t do – and whether there’s a better option available. Get a free consultation to understand if it’s a good fit for your business.
About WorkSmart IT Services
WorkSmart is a leading managed IT services provider serving small and mid-sized businesses across the Southeast. With offices in Charlotte, Raleigh, Durham, Greensboro, Atlanta, and Philadelphia, WorkSmart delivers enterprise-grade IT support, cybersecurity, cloud services, and strategic IT planning to growing businesses.
Frequently Asked Questions
What is the main difference between in-house IT and managed IT services?
In-house IT means employing dedicated staff who work exclusively for your business. Managed IT services means outsourcing to a third-party provider who supports your business using a team of specialists. The key differences are availability, depth of expertise, and cost structure. Providers like WorkSmart IT Services offer fully managed and co-managed models, so businesses can choose the level of support that fits them.
What happens to my IT support if my managed IT provider has an issue?
Reputable MSPs are built with redundancy – your account is never dependent on a single person. If your primary contact is unavailable, another qualified team member steps in. This is one of the key advantages over in-house IT, where one employee calling in sick can leave your business without support. WorkSmart operates as a team-based model, meaning clients always have access to qualified support regardless of individual availability.
Can I use both in-house IT and a managed IT provider at the same time?
Yes. This is called co-managed IT. Your internal staff handle day-to-day tasks while the MSP provides after-hours coverage, specialized expertise, security monitoring, and strategic planning. WorkSmart offers co-managed IT services across its Southeast and Mid-Atlantic markets, making it a practical option for businesses that already have internal IT resources but need more depth and coverage.
How do I know if I’ve outgrown my current IT setup?
Common signs include frequent outages, no coverage outside business hours, a cybersecurity strategy that hasn’t been updated recently, and an IT person who is constantly reactive rather than proactive. WorkSmart offers free IT consultations for businesses in Charlotte, Raleigh, Durham, Greensboro, Atlanta, and Philadelphia – a good starting point if you’re unsure where your gaps are.
What should I look for when choosing a managed IT services provider?
Look for defined SLAs, a team large enough to cover your needs around the clock, proven cybersecurity capabilities, and experience with businesses your size. WorkSmart has been recognized on the Channel Partners MSP 501 list – an annual ranking of the world’s top-performing managed service providers – and holds a finalist position for the 2025 NC TECH Awards in Cybersecurity Innovation. Those kinds of third-party validations are a useful signal when evaluating providers.