It doesn’t. There are critical tools every organization needs in place to protect against cyber threats. Firewalls, anti-virus software, managed DNS, and encryption are a few you may already be using. But no protection is 100% effective at stopping hackers, because the bad guys are evolving their tools as often as the good guys are developing protections.
A layered defense is standard for all organizations, big and small. And hackers know you have a lot of defenses in place working together. But the one thing that has been consistently successful for the bad guys is email.
It’s easier for a bad guy to convince someone to open the door to your house than to break in.
No security tool can stop all phishing emails. And unless users are aware and vigilant all the time, it only takes one click on one malicious link to let a hacker in your network.
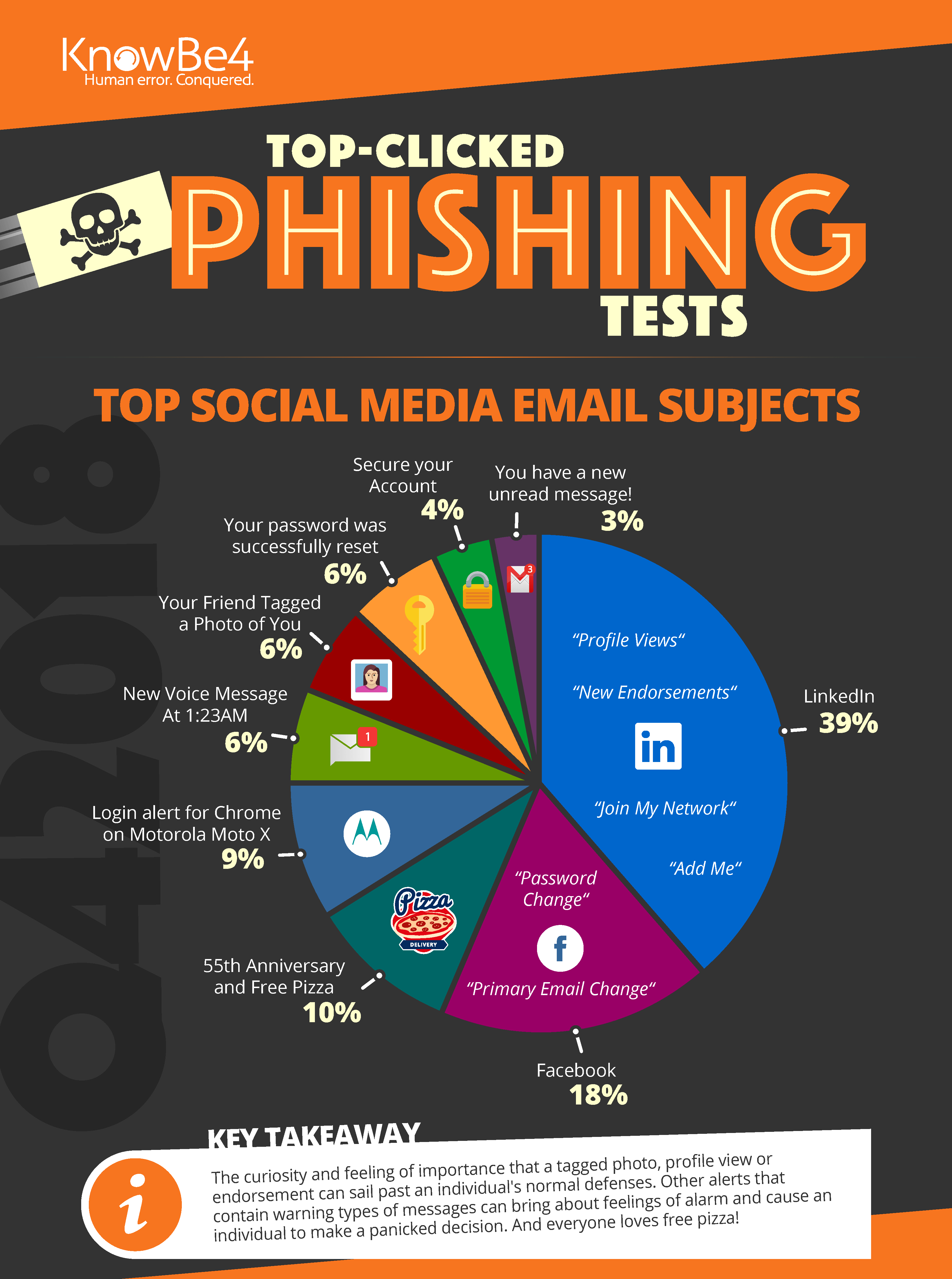
Everyone loves free pizza
Our partner KnowBe4 released the most-clicked email subjects last quarter (infographic below), and it’s worth reviewing to see what you may have been exposed to (or even clicked on). If you use LinkedIn, you know that LinkedIn sends a lot of emails with links to find out more about profile views, comments on your posts, or someone wanting to connect with you. Do you pause and look for signs that it’s a phishing email before you click? Fake LinkedIn emails were the largest percentage of clicked phishing tests by users. Followed by Facebook emails and links for free pizza.
The only defense against phishy free pizza emails is regular Security Awareness Training for your staff.
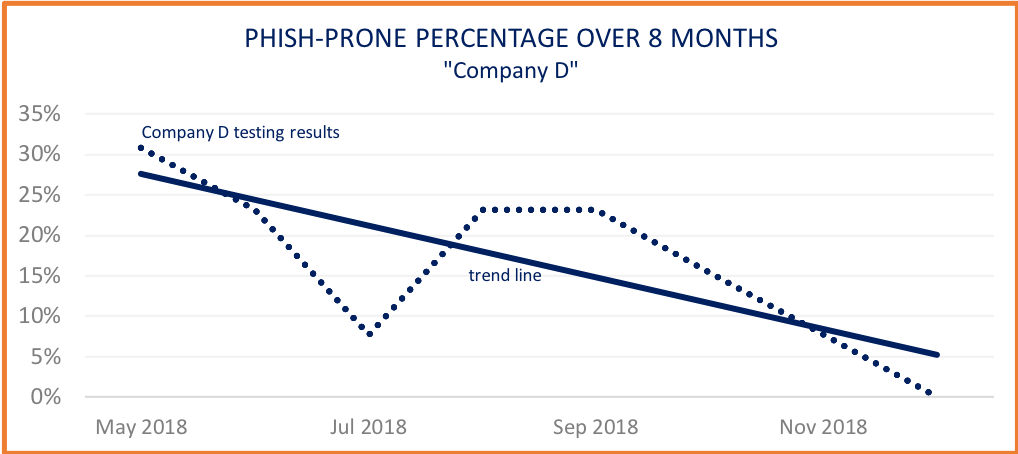
The good news is that most of our clients have Security Awareness Training service in place. And we can look at the results to see how employees got savvy about phishing emails. Check out one of our clients below (we’ll call it “Company D”). Their phish-prone percentage dropped from 30% to 0% over eight months, with a bump up in July when we onboarded new employees to the training program.
If I click on a link and then realize it may have been malicious, what do I do?
Quickly alert your internal IT manager, and call WorkSmart. In some cases, we can minimize damage by resetting passwords so the hacker can’t get inside your email to send “real” emails that can cost your organization. But if clicking that link put malicious code on your machine, we’ll need to take other actions to try and keep your organization safe.
Get an overview of our Security Awareness Training service here, and keep an eye out for more cybersecurity updates from WorkSmart.