Phishing attacks take advantage of people by posing as a trusted source. Not surprisingly, cybercriminals are using concerns about coronavirus to attack businesses. Unfortunately, they’re using fear as bait.
Cybercriminals easily steal passwords. That’s why the number of attacks continues to rise. Most often, a phishing attack will trick you into handing over your username and password. By clicking a link, you may be prompted to enter your login into a fake site. Or it installs a program to log keystrokes, ultimately capturing your login.
Here’s one of the Coronavirus phishing attacks.
We’ve seen these phishing emails in action, and they’re convincing.
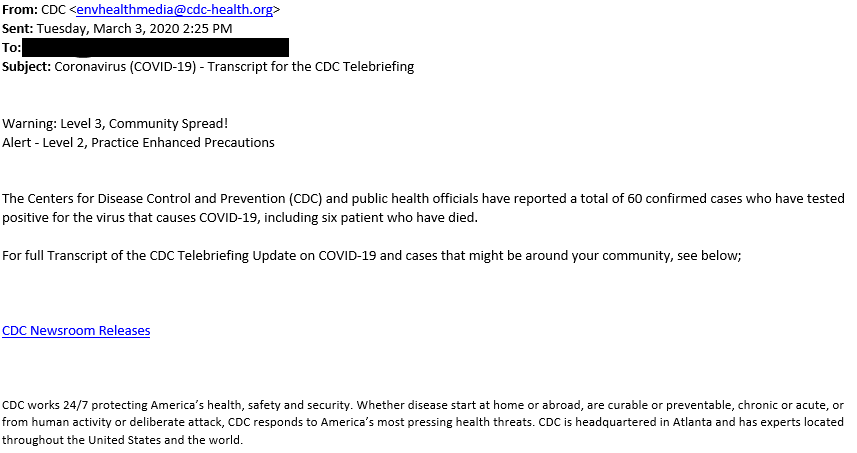
This one appears to come from the Centers for Disease Control & Prevention (CDC), informs recipients of an increase in the total number of confirmed cases, and provides a link to the CDC website for more details.
How do I know these are phishing attacks?
Pause, pay attention to the details, and look for these signs before you click.
- the sender’s email address – this one came from cdc-health.org, but the CDC’s real domain is cdc.gov.
- the URL of the link – when you hover over it, the real address doesn’t match where it claims to send you. The CDC Newsroom is at https://www.cdc.gov/media/archives.html.
Be safe. Don’t click the link. Don’t enter any credentials. Don’t download any attachments. Don’t send any money without proper verification.
If I click on a link and then realize it was a phishing attack, what do I do?
Quickly alert your IT team. In some cases, you can minimize damage by resetting passwords so the hacker can’t get inside your email to send “real” emails from your account. But if clicking that link put malicious code on your machine, you’ll need to take other immediate actions to reduce the risk. Either way, alert your IT team as quickly as possible.
What can I do to stop phishing attacks like these?
No single security tool can prevent phishing attacks – the best cybersecurity plan uses layers of security. For scams like these, you can help protect yourself by:
- educating your users so they know what to look for and keep security top-of-mind
- protecting your data using multi-factor authentication, which will stop the bad guys even if they know your password
Employee Education
The number one security risk for businesses isn’t their technology—it’s their end users.
Security Awareness Training trains non-technical employees to spot the signs of a malicious email so they don’t click a link that could ruin everyone’s day. 
Security awareness training also covers topics like password security, safe web browsing, and mobile device security so your employees stay up-to-date and vigilant about protecting their organization. And because cybersecurity threats change all the time, the training modules are updated regularly by expert cybersecurity teams.
One of our Raleigh-based clients saw their phish-prone percentage fall from 51% to 2% after training. As a recruiting firm, their end-users send and receive a LOT of email. The whole organization really got into it. Users still forward suspicious emails to get checked out, staying constantly vigilant.
Multi-factor Authentication
Unless users are aware and vigilant all the time, it only takes one click on a malicious link to let a hacker in your network. With multi-factor authentication, you add a second step to verify a user’s identity. The use of additional authentication information makes it much harder to log in as you.
Here’s how it works: after you enter your password at login, you’ll be asked for a second piece of information, most typically a one-time code generated on-the-spot and sent by SMS to the user’s cell phone.


