More data than ever is being created and stored due to the increased use of technology in everyday business operations. Add to that the need for data to be accessible in the cloud so that people can access what they need, no matter where they’re working from.
With a surge in data volume and greater accessibility to that data, it’s more important than ever to ensure that your organization takes the necessary precautions to keep your information secure. On the flip side, you don’t want to cause frustration among your team members with a time-consuming authentication process.
Microsoft Azure’s Conditional Access is a proven tool that balances keeping your security standards high without excessively burdening your team with requirements.
Source: Microsoft Documentation
What is Conditional Access?
Conditional Access is a key feature of Microsoft Azure Active Directory. Its policies are intended to safeguard the authentication process to help minimize the risk of an unauthorized user accessing data, potentially resulting in a massive data breach.
Think about how you’ve always logged in to your accounts. You typically have a unique username and password that grants you access to everything within that account. Now, suppose a hacker was able to compromise that username and password combination. They would then have access to everything that lives in that account as well, which is not a situation you want to find yourself in.
With Conditional Access, specific policies are put in place to strengthen your authentication process while simultaneously avoiding too much frustration for your team.
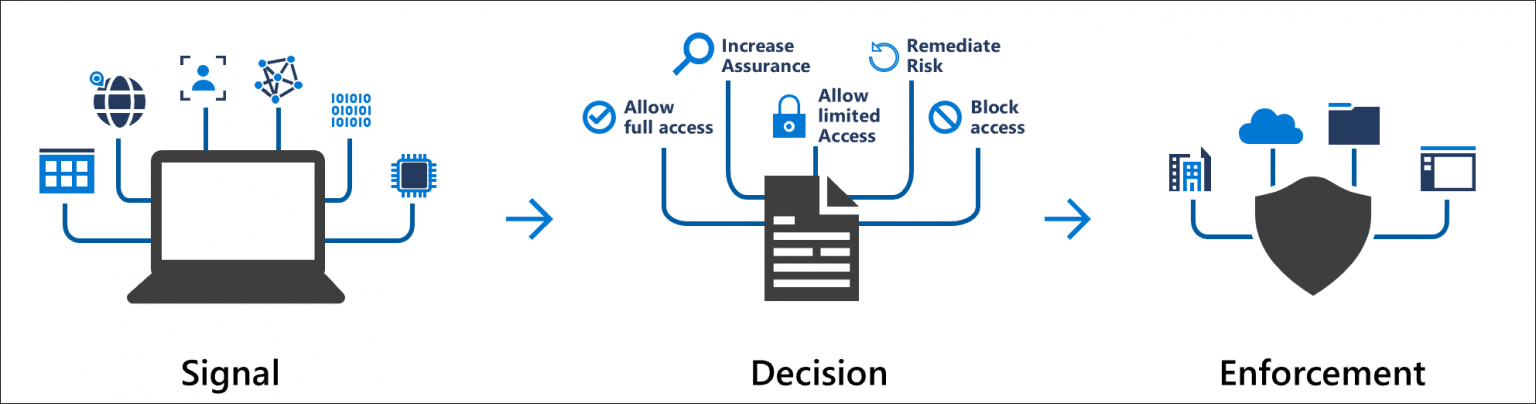
At its root, Conditional Access uses if-then statements to determine how much access a user should get. Once certain conditions are met, the user is granted access to only what they need. Let’s look a little further into how this plays out.
How Does It Work?
These if-then statements consist of specific requirements that must be met in order to determine the appropriate level of access permitted. Simply stated, if someone wants to access a resource, they must complete a specific action to do so. The triggers that prompt a Conditional Access policy for authentication are often referred to as signals.
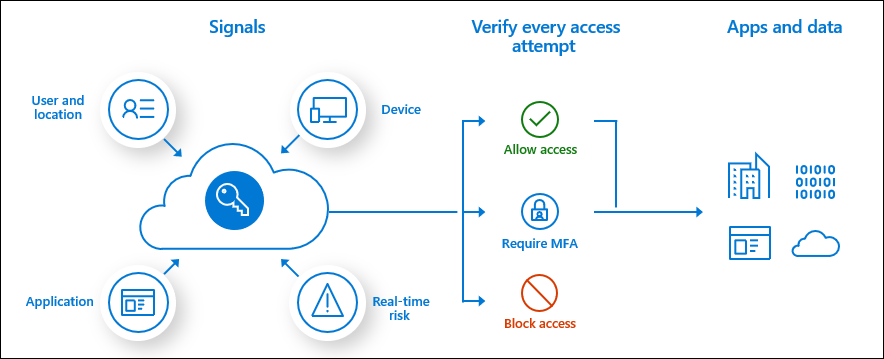
There are a few standard signals that businesses tend to use when determining the appropriate access policies:
Users and Groups:
Policies can be tailored towards specific users or groups of users within your organization. For example, team members who need to access payroll information may be categorized into one group. When those individuals make an authentication attempt to gain access to payroll data, they would then be prompted to complete the actions specified for that access.
IP Location:
Depending on where your business is located, it may make sense for you to create trusted IP address ranges to limit traffic into your system. For example, if you know that you have absolutely no business in a specific country, you could set a policy to deny access to users attempting to log in with an IP address coming from that country.
Applications:
Another standard signal to trigger a Conditional Access policy is through a specific application. For example, when a user attempts to log in to an Office 365 application, a Conditional Access policy can be implemented to require additional authentication before gaining access. Similar policies can be created for any other apps you want to further protect as well.
Devices:
Conditional access policies can also be triggered by specific devices being used. For example, if someone is attempting to log in to a workstation with privileged access, a policy could be created to require further authentication before gaining access to the workstation itself.
Source: Microsoft Documentation
Your signals are in place… what’s next?
Once you’ve selected your signals to trigger Conditional Access policies, the next step is to determine the appropriate action that the user must complete to gain access.
Multi-factor authentication (or MFA) is one of the most common identity verification mechanisms. Let’s say you want to ensure security when your team is using Office 365, so you set a signal to trigger a Conditional Access policy anytime someone attempts to log in to the platform. If MFA was set as the required action, users would have to complete the extra step while logging in to prove their identity.
Another common mechanism used within Conditional Access policies is to simply block access. As mentioned above, if you know there are locations that you have no business in or devices that your organization does not manage, you can prohibit those log-in attempts. While this is the most restrictive option, it helps ensure that only authorized people are accessing your data.
When it comes to deciding the appropriate actions for users to verify their identity, you have options. Azure AD’s Conditional Access provides a wide range of requirements that can be put in place to help keep your organization’s data secure from unauthorized users.
Working smart to protect your data.
Protecting your organization’s data should be top of mind, especially as we shift to the cloud and legal requirements continue to increase. Balancing security and convenience can be difficult, but not if you have the proper tools in place. Azure AD’s Conditional Access not only adds another layer of protection over your data but also keeps the login process quick and simple for your team.
Conditional Access is not meant to be your one and only defense mechanism but rather an additional layer of security that doesn’t slow down your team’s productivity in the meantime.
Contact us today if you’d like to learn more about keeping your organization secure!